Triggers
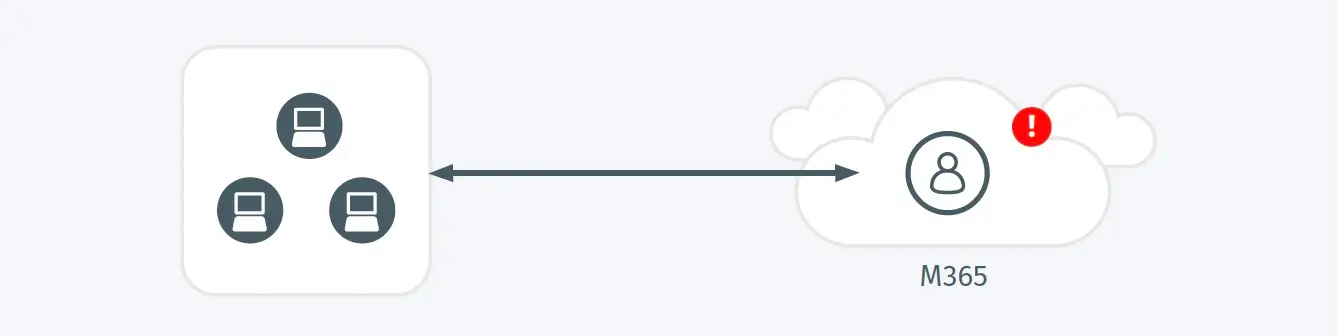
- A rarely used, third-party Microsoft Teams integrated application has been granted excessive or risky permissions that may enable malicious activities to be taken on behalf of the authorizing user
Possible Root Causes
- An attacker is trying to trick the user into authorizing a third-party app that will allow the the attacker to execute malicious actions.
- In some cases rare, legitimate applications do require a set of permissions that are authorized despite the risk they present.
Business Impact
- Malicious third-party apps can be used to undermine existing security controls, such as multi-factor authentication (MFA), and enable malicious action on behalf of the authorizing user, increasing risk to enterprise system and data and increasing the likelihood of further attack progression.
- A suspicious teams application could result in outcomes ranging from the compromise of an individual account or host, to broader compromise of a full teams channel.
- Malicious apps may enable a foothold into the environment as a means of maintaining persistent access.
- Malicious apps could may allow the collection of sensitive information or act as a mechanism to support data exfiltration.
Steps to Verify
- Verify that the application in question is authorized for the associated user.
- Validate that the required permission set is appropriate for the authorized business process associated with this application.
- Investigate for additional malicious indicators associated with this application or user.