Spiegazione delle minacce persistenti avanzate (APT): le minacce informatiche provenienti da Stati-nazione che i difensori devono comprendere
Approfondimenti chiave
- Gli APT sono caratterizzati da tre elementi distintivi: tecniche avanzate, accesso persistente a lungo termine (con una permanenza media di 95 giorni) e attori malintenzionati dotati di ingenti risorse finanziarie e con obiettivi strategici specifici, quali lo spionaggio o il sabotaggio.
- L'identità è ormai il vettore di attacco predominante. Secondo una ricerca condotta da Unit 42, le vulnerabilità relative all'identità hanno avuto un ruolo determinante in quasi il 90% delle indagini, con il 65% degli accessi iniziali basati proprio sull'identità.
- Le operazioni APT stanno accelerando. Le campagne più rapide passano ora dall'accesso iniziale all'esfiltrazione dei dati in soli 72 minuti, quattro volte più velocemente rispetto all'anno precedente.
- Una difesa efficace richiede controlli a più livelli che combinino il rilevamento comportamentale delle minacce, il monitoraggio delle identità, il rilevamento e la risposta a livello di rete e le informazioni sulle minacce, piuttosto che affidarsi a un unico strumento.
- Nessun concorrente offre una visione completa della situazione. Le tattiche APT Cloud, i modelli di attacco incentrati sull'identità, il rilevamento potenziato dall'intelligenza artificiale e la mappatura dei quadri normativi sono lacune fondamentali che questa guida si propone di colmare.
Una minaccia persistente avanzata non è un'operazione lampo. Si tratta di una campagna che dura mesi, condotta da alcuni degli avversari più ben equipaggiati del pianeta: Stati-nazione e gruppi sponsorizzati dallo Stato che dispongono della pazienza, dei fondi e delle competenze necessarie per infiltrarsi in una rete, rimanere inosservati ed estrarre esattamente ciò che sono venuti a cercare. Solo nel 2025, la Salt Typhoon ha compromesso più di 600 organizzazioni in 80 paesi, mentre il Lazarus Group ha eseguito una rapina di criptovalute da 1,5 miliardi di dollari attraverso una singola compromissione della catena di approvvigionamento. Il mercato della protezione dalle minacce persistenti avanzate (APT) ha raggiunto circa 9,2 miliardi di dollari, riflettendo la portata del problema che le organizzazioni devono affrontare oggi. Questa guida spiega cosa sono le APT, come operano, quali gruppi sono più attivi e, cosa più importante per chi si occupa di difesa, come individuarle e fermarle.
Che cos'è una minaccia persistente avanzata (APT)?
Una minaccia persistente avanzata (APT) è un attacco informatico sofisticato e prolungato in cui un avversario dotato di risorse adeguate — in genere uno Stato-nazione o un gruppo sponsorizzato dallo Stato — ottiene l'accesso non autorizzato a una in cui un avversario dotato di risorse adeguate — in genere uno Stato-nazione o un gruppo sponsorizzato dallo Stato — ottiene l'accesso non autorizzato a una rete e mantiene una presenza nascosta per un lungo periodo al fine di rubare dati, condurre attività di spionaggio o operazioni di sabotaggio.
Il Centro risorse per la sicurezza informatica del NIST definisce un APT come «un avversario che possiede competenze di alto livello e risorse significative che gli consentono di creare opportunità per raggiungere i propri obiettivi utilizzando molteplici vettori di attacco». Questa definizione formale coglie le tre caratteristiche che distinguono gli APT dagli attacchi informatici convenzionali.
Avanzato. Gli autori delle minacce APT utilizzano malware personalizzato, zero-day e sofisticate tecniche di elusione. Adattano i propri strumenti nel corso della campagna quando i difensori individuano singoli componenti.
Persistenza. Il tempo di permanenza — ovvero il lasso di tempo che intercorre tra la compromissione iniziale e il rilevamento — è in media di 95 giorni per le operazioni APT, con alcune campagne che si protraggono per oltre un anno. La campagna Salt Typhoon è rimasta attiva per uno o due anni prima di essere scoperta. Ciò è in netto contrasto con il tempo di permanenza mediano degli attacchi informatici, pari a otto giorni.
Minaccia. Gli APT sono avversari umani organizzati e ben finanziati, con obiettivi specifici. A differenza dei criminali informatici opportunisti che sfruttano qualsiasi vulnerabilità trovino, i gruppi APT prendono di mira organizzazioni specifiche per raggiungere obiettivi strategici: furto di proprietà intellettuale, spionaggio politico, sabotaggio di infrastrutture critiche o furti finanziari su larga scala.
Caratteristiche principali di un attacco APT
Le caratteristiche distintive di un attacco APT includono il sostegno da parte di uno Stato-nazione o di soggetti sponsorizzati dallo Stato, una metodologia di attacco in più fasi che si sviluppa nell’arco di settimane o mesi, obiettivi strategici specifici che vanno oltre il mero guadagno economico, l’uso di strumenti personalizzati e zero-day , nonché la capacità di adattarsi e ristabilire la persistenza anche dopo un rilevamento parziale. Gli APT si differenziano inoltre dal malware standard malware quanto sono operazioni dirette dall'uomo. Mentre malware routine automatizzate, gli operatori APT prendono decisioni in tempo reale, cambiano strategia in base a ciò che scoprono e adattano le loro tecniche per eludere le difese specifiche che incontrano. Comprendere queste caratteristiche è essenziale per costruire difese all'altezza della sofisticazione della minaccia.
Come funzionano gli attacchi APT: il ciclo di vita degli attacchi APT
Gli attacchi APT seguono un ciclo di vita articolato in più fasi che può protrarsi da settimane ad anni. Sebbene esistano vari modelli che descrivono questo processo in modi diversi — da schemi in tre fasi a modelli strutturati in sette fasi — il seguente ciclo di vita in sei fasi riassume le fasi essenziali che gli addetti alla sicurezza devono comprendere.
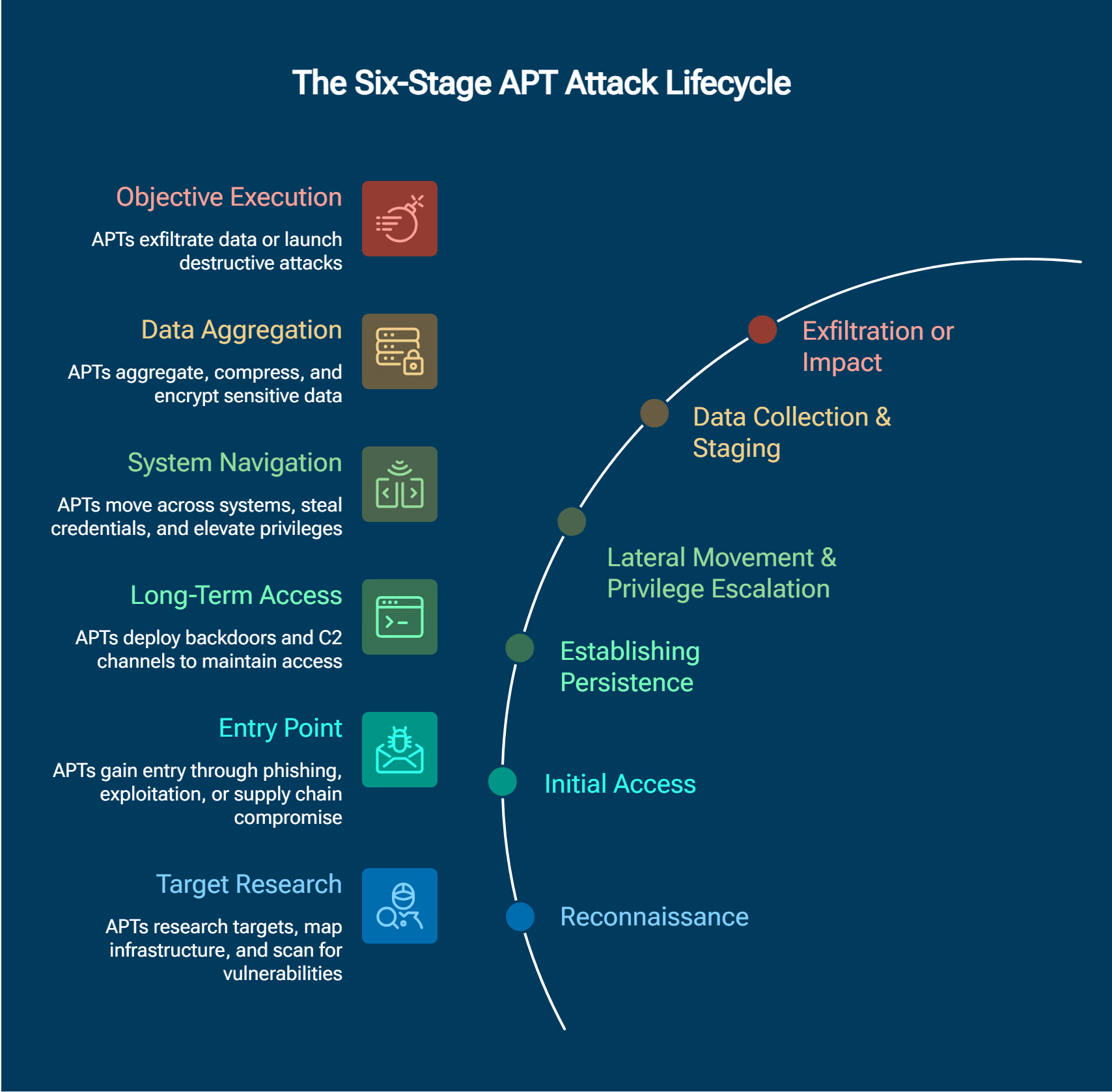
- Ricognizione — Analisi degli obiettivi, mappatura delle infrastrutture e scansione delle vulnerabilità per individuare i punti di accesso e le risorse di alto valore.
- Accesso iniziale — Secondo la ricerca condotta da Unit 42 nel 2026, phishing spear phishing e lo sfruttamento delle vulnerabilità sono in testa alla classifica dei vettori di accesso iniziale, entrambi al 22%. Gli attacchi APT sfruttano inoltre zero-day , compromissioni della catena di approvvigionamento e vulnerabilità dei dispositivi periferici presenti in router e apparecchiature VPN.
- Assicurarsi la persistenza — Gli aggressori installano backdoor, rootkit e canali di comando e controllo (C2) per mantenere l'accesso anche nel caso in cui il punto di ingresso iniziale venga scoperto e chiuso.
- Movimento laterale e escalation dei privilegi — Gli operatori si spostano tra i segmenti di rete sfruttando credenziali rubate e l'identità degli utenti, alla ricerca di un accesso privilegiato e di obiettivi di maggior valore.
- Raccolta e preparazione dei dati — Gli autori degli attacchi individuano, raccolgono e preparano i dati di alto valore in vista del loro prelievo, spesso comprimendoli e crittografandoli per evitare di essere scoperti.
- Esfiltrazione o impatto — Furto di dati, spionaggio, sabotaggio tramite attacchi wiper o frodi finanziarie. La rapina ai danni di Bybit perpetrata dal Gruppo Lazarus e gli attacchi wiper ZEROLOT di Sandworm rappresentano i due estremi opposti di questa fase finale.
Nei casi più rapidi osservati, l'intera sequenza, dall'accesso iniziale all'esfiltrazione, richiede ora solo 72 minuti — quattro volte più veloce rispetto all'anno precedente, secondo il Rapporto globale sulla risposta agli incidenti 2026 di Unit 42.
L'identità come principale vettore di attacco APT
Nel 2025 e nel 2026, le vulnerabilità relative all'identità sono diventate il vettore di attacco APT predominante. La ricerca condotta da Unit 42 dimostra che tali vulnerabilità hanno avuto un ruolo determinante in quasi il 90% delle indagini e che il 65% degli accessi iniziali è ora basato sull'identità. Ciò rappresenta un cambiamento fondamentale nel modo in cui operano gli attacchi APT.
Le moderne campagne APT sfruttano il furto di credenziali, la manipolazione dei token, la compromissione dei servizi di directory e l'uso improprio di identità non umane, prendendo di mira le chiavi API, gli account di servizio e i token OAuth su cui fanno affidamento i sistemi automatizzati. Anziché distribuire malware personalizzato malware fa scattare endpoint , i gruppi più sofisticati effettuano l'accesso con credenziali legittime e operano attraverso l'infrastruttura delle identità, rendendo il rilevamento molto più difficile per gli strumenti di sicurezza tradizionali.
Strumenti e tecniche APT
I gruppi APT utilizzano diverse categorie di strumenti per minacce persistenti avanzate, tutti progettati per eludere il rilevamento.
- malware personalizzato — Impianti creati appositamente, come TernDoor e PeerTime Salt Typhoon o GearDoor di Silver Dragon, progettati per obiettivi e campagne specifici
- Tecniche "living-off-the-land" — Utilizzo di strumenti di sistema legittimi già presenti nell'ambiente per evitare l'introduzione malware rilevabile
- Strumenti legittimi di accesso remoto — Utilizzo improprio di software autorizzati per l'amministrazione remota al fine di ottenere un accesso non autorizzato
- AbusoCloud — Sfruttamento cloud per le comunicazioni C2, come nel caso di Silver Dragon (APT41) che ha utilizzato Google Drive per le operazioni C2
Per i responsabili della sicurezza, l'importante è comprendere queste categorie per elaborare strategie di rilevamento adeguate, non gli strumenti specifici in sé. Il modello della «cyber kill chain» fornisce ulteriori indicazioni su come questi strumenti si rapportino alle diverse fasi dell'attacco.
Gruppi APT ed esempi concreti
Gruppi attivi specializzati in minacce persistenti avanzate (APT) continuano a prendere di mira i settori delle telecomunicazioni, della pubblica amministrazione, dell'energia e della finanza con campagne sempre più sofisticate. Secondo i rapporti di intelligence sulle minacce del settore, la Cina e la Corea del Nord sono responsabili del 55% degli attacchi APT a livello mondiale.
Salt Typhoon RPC/MSS). Questo gruppo cinese finanziato dallo Stato ha condotto la più significativa campagna di spionaggio nel settore delle telecomunicazioni della storia recente, compromettendo oltre 600 organizzazioni in 80 paesi, tra cui nove società di telecomunicazioni statunitensi e i sistemi di intercettazione CALEA. Nel 2026, Salt Typhoon ha esteso le proprie operazioni alle società di telecomunicazioni sudamericane con nuovi strumenti di infiltrazione, tra cui TernDoor, PeerTime e BruteEntry.
Lazarus Group (Corea del Nord). Il gruppo APT più attivo della Corea del Nord ha messo a segno la rapina da 1,5 miliardi di dollari alla piattaforma di criptovalute Bybit sfruttando una vulnerabilità nella catena di approvvigionamento dell'ambiente di sviluppo di Safe{Wallet}: si tratta del più grande furto finanziario APT mai registrato.
APT41/Silver Dragon (RPC). Questo gruppo con doppia missione ha condotto attività di spionaggio ai danni di governi europei utilizzando una backdoor denominata GearDoor con Google Drive come server di comando e controllo (C2), mettendo in evidenza tecniche di attacco cloud.
Sandworm/APT44 (Russia/GRU). L'APT dei servizi di intelligence militare russi ha sferrato attacchi di tipo "wiper" tramite ZEROLOT contro le infrastrutture energetiche ucraine e ha tentato attacchi simili ai sistemi energetici polacchi, continuando a concentrarsi sul sabotaggio delle infrastrutture critiche.
Il rapporto " ENISA Threat Landscape 2025 " ha documentato 4.875 incidenti nell'UE nel periodo compreso tra luglio 2024 e giugno 2025, durante il quale attori legati a entità statali hanno intensificato campagne di spionaggio a lungo termine. L'Agenzia per la sicurezza informatica di Singapore ha avviato l'operazione CYBER GUARDIAN in risposta all'attacco alle telecomunicazioni sferrato da UNC3886, schierando oltre 100 esperti di sicurezza informatica.
Gruppi APT in base all'attribuzione a uno Stato-nazione
Tabella: "Principali gruppi APT attivi nel periodo 2025–2026 con attribuzione a Stati nazionali e campagne recenti". Testo alternativo: "Tabella che elenca i principali gruppi APT suddivisi per attribuzione a Stati nazionali, compresi i loro obiettivi principali e le recenti attività di campagna".
Questi gruppi APT rappresentano solo le operazioni più evidenti. Esistono centinaia di altri gruppi che operano con vari livelli di sostegno da parte degli Stati, e il confine tra gli APT sponsorizzati dagli Stati e le sofisticate organizzazioni di criminali informatici continua a diventare sempre più labile. Per un'analisi più approfondita di specifici attori delle minacce, consulta le risorse Vectra AI dedicate agli attori delle minacce informatiche e la copertura delle recenti violazioni dei dati.
Le APT nella pratica: impatto sul business e tendenze
Gli APT operano oggi a una velocità quattro volte superiore rispetto a un anno fa, sfruttano sempre più le infrastrutture cloud di gestione delle identità e utilizzano l'intelligenza artificiale per estendere le loro operazioni a centinaia di organizzazioni contemporaneamente.
L'impatto finanziario delle campagne APT varia da milioni di dollari in costi di indagine e riparazione a perdite catastrofiche causate da un singolo evento. Il furto da 1,5 miliardi di dollari ai danni di Bybit perpetrato dal Lazarus Group rappresenta il singolo evento APT con il maggiore impatto finanziario. Le organizzazioni stanno reagendo: il mercato della protezione contro le APT ha raggiunto circa 9,2 miliardi di dollari nel 2025 e sta crescendo a un tasso di crescita annuale composto (CAGR) del 19,9%, a testimonianza dell'escalation della minaccia.
Le tecniche di attacco potenziate dall'intelligenza artificiale stanno trasformando le operazioni APT. Secondo il rapporto "Threat Landscape 2025" dell'ENISA, oltre l'80% delle phishing integra ormai contenuti generati dall'intelligenza artificiale. APT36 è diventato il primo attore statale documentato a utilizzare l'IA come "catenamalware ", accelerando la produzione di malware polimorfico. Nel frattempo, il 48% dei professionisti della sicurezza informatica classifica l'IA agentica come il principale vettore di attacco per il 2026, riconoscendo che gli agenti di IA introducono nuove identità non umane e ampliano le superfici di attacco alla sicurezza dell'IA.
Modelli APT specifici per le applicazioni Cloud e SaaS
Gli attacchi APT prendono sempre più di mira cloud utilizzando tecniche progettate specificamente per le infrastrutture cloud. Tra queste figurano l'abuso della federazione delle identità per spostarsi tra cloud on-premise e cloud , il furto di token OAuth per ottenere un accesso persistente alle applicazioni SaaS, la compromissione della catena di fornitura SaaS attraverso strumenti di sviluppo e pipeline di compilazione, nonché il riutilizzo cloud per le comunicazioni C2.
La campagna Silver Dragon è un chiaro esempio di questa tendenza, poiché utilizza Google Drive come canale di comando e controllo che si mimetizza nel normale traffico aziendale. APT31 ha sfruttato i servizi cloud per le operazioni di comando e controllo, approfittando della fiducia che le organizzazioni ripongono nei cloud legittimi. Con l'accelerazione cloud da parte delle aziende, queste tecniche diventeranno sempre più diffuse, rendendo necessarie capacità di rilevamento che coprano l'identità, la rete e cloud .
Individuazione e prevenzione delle minacce APT
Una difesa efficace contro le minacce APT richiede controlli a più livelli che combinino analisi comportamentali, monitoraggio delle identità, rilevamento e risposta a livello di rete, intelligence sulle minacce e rafforzamento della sicurezza dei dispositivi periferici, piuttosto che affidarsi a un unico strumento o approccio.
Analisi comportamentale e NDR. Il monitoraggio continuo del traffico di rete rileva i comportamenti successivi alla compromissione che caratterizzano gli attacchi APT — spostamenti laterali, comunicazioni C2 e preparazione dei dati — che gli strumenti basati su firme spesso non individuano. Il sistema di rilevamento e risposta di rete (NDR) offre visibilità su questi comportamenti nell'intera rete, compreso il traffico crittografato.
Monitoraggio delle identità. Considerando che nel 90% delle indagini sulle minacce APT emergono vulnerabilità relative alle identità e che il 65% degli accessi iniziali avviene tramite l'uso delle identità, il rilevamento e la risposta alle minacce legate alle identità non sono più facoltativi. È necessario monitorare la presenza di modelli di autenticazione anomali, la manipolazione dei token, la compromissione dell'SSO e la persistenza degli accessi privilegiati.
Ricerca delle minacce. Attività di ricerca proattiva e regolare, incentrata sui modelli di movimento laterale e sugli indicatori C2, aiuta a individuare attività APT che gli strumenti automatizzati potrebbero non rilevare.
Rafforzamento della sicurezza dei dispositivi periferici. Router, firewall e dispositivi VPN sono sempre più spesso presi di mira come punti di accesso iniziali, come dimostrato dalle campagne Salt Typhoon UNC3886. La visibilità a livello di rete su questi dispositivi è fondamentale.
Operatività delle informazioni sulle minacce. Utilizzare i flussi di informazioni sulle minacce provenienti dalla CISA e da fonti del settore e agire di conseguenza. Raccogliere informazioni senza metterle in pratica crea un falso senso di preparazione.
Preparazione alla risposta agli incidenti. Mantenere backup offline e piani di risposta agli incidenti collaudati, specificamente progettati per scenari APT distruttivi come gli attacchi wiper.
Indicatori di una compromissione da parte di un attacco APT
I responsabili della sicurezza dovrebbero prestare attenzione ai seguenti segnali di attività legate alle minacce persistenti avanzate:
- Modelli di traffico in uscita insoliti, in particolare trasferimenti di grandi quantità di dati verso destinazioni sconosciute
- Eventi di autenticazione anomali, tra cui accessi al di fuori dell'orario di lavoro e scenari di spostamento impossibili
- Archiviazione o compressione inattesa dei dati in directory insolite
- Meccanismi di persistenza quali nuove attività pianificate, modifiche al Registro di sistema o servizi non autorizzati
- Richieste DNS anomale che indicano un comportamento di tunneling o beaconing del DNS
- Indicatori di spostamento laterale, compreso l'uso anomalo di protocolli di amministrazione remota
Creare una difesa a più livelli contro gli attacchi APT
Non esiste uno strumento unico in grado di bloccare gli attacchi APT. L'approccio più efficace consiste nell'integrare la tecnologia NDR con EDR e SIEM per garantire una copertura completa della rete, endpoint e dei dati di telemetria dei log. Applicare zero trust per limitare l'estensione dell'impatto. Rendere obbligatoria l'autenticazione a più fattori su tutti i punti di accesso. Implementare un monitoraggio continuo anziché valutazioni periodiche.
Tabella: "Lista di controllo per il rilevamento delle APT destinata ai team SOC, relativa endpoint di rete, delle identità e endpoint ."
APT e quadri normativi
Il documento NIST SP 800-172 fornisce controlli di sicurezza avanzati specificamente progettati per la difesa dalle minacce APT (Advanced Persistent Threat) delle informazioni controllate non classificate (CUI) contro le minacce provenienti da Stati-nazione. I suoi principi fondamentali — doppia autorizzazione, segmentazione della rete, monitoraggio continuo e principio del privilegio minimo — affrontano direttamente la persistenza e la sofisticatezza che caratterizzano le operazioni APT.
MITRE ATT&CK mappa i comportamenti delle APT in tutte le 14 tattiche aziendali, fornendo un linguaggio comune per l'ingegneria del rilevamento. Le principali tecniche rilevanti per le APT includono T1566 (Phishing), T1547 (Esecuzione automatica all'avvio o all'accesso), T1021 (Servizi remoti), T1071 (protocollo a livello di applicazione per il C2), e T1041 (Esfiltrazione tramite canale C2). Il testo completo MITRE ATT&CK fornisce una mappatura a livello tecnico per la creazione di regole di rilevamento.
Tabella: "Mappatura del quadro normativo e di conformità per la difesa contro gli attacchi APT". Testo alternativo: "Tabella che mette in relazione i requisiti di difesa contro gli attacchi APT con lo standard NIST SP 800-172, MITRE ATT&CK, la norma ISO 27001, i controlli CIS e le linee guida della CISA."
Le organizzazioni soggette a quadri normativi di conformità dovrebbero allineare i propri programmi di difesa contro le minacce APT a tali quadri di sicurezza, al fine di garantire sia l'efficacia operativa che la preparazione alle verifiche.
Approcci moderni alla difesa contro le APT
Il settore sta evolvendo le difese contro le minacce APT oltre i confini della tradizionale sicurezza perimetrale. Poiché le minacce APT operano sempre più spesso attraverso l'abuso di identità piuttosto che malware un cambiamento documentato da Intelligent CISO — gli addetti alla sicurezza necessitano di capacità di rilevamento comportamentale che coprano cloud relativa a identità, rete e cloud .
Le moderne soluzioni contro le minacce persistenti avanzate si basano su tre funzionalità principali. In primo luogo, il rilevamento delle minacce basato sull'intelligenza artificiale, che identifica i comportamenti degli aggressori in tempo reale anziché fare affidamento su firme note. In secondo luogo, il rilevamento e la risposta alle minacce relative alle identità, che monitora l'uso improprio delle credenziali, la manipolazione dei token e i modelli di accesso anomali a livello delle identità. In terzo luogo, la copertura unificata della superficie di attacco, che mette in correlazione i segnali provenienti da reti locali, cloud , sistemi di gestione delle identità e applicazioni SaaS.
Vectra AI alla difesa contro le APT
L'approccio Vectra AI alla difesa contro le APT si basa sulla filosofia del "presupporre la compromissione". Poiché gli aggressori più sofisticati finiranno inevitabilmente per ottenere l'accesso, la capacità fondamentale consiste nell'individuare i loro comportamenti successivi alla compromissione — spostamenti laterali, escalation dei privilegi, comunicazioni C2 e preparazione dei dati — attraverso un Attack Signal Intelligence basato sull'intelligenza artificiale Attack Signal Intelligence mette in correlazione i segnali provenienti dall'intera rete moderna. Ciò significa una copertura che abbraccia ambienti on-premise, cloud, di identità e SaaS attraverso la Vectra AI , consentendo ai team SOC di individuare e bloccare gli operatori APT prima che raggiungano i loro obiettivi, anche quando tali operatori utilizzano credenziali legittime e tecniche "living-off-the-land" che aggirano le difese tradizionali.
Tendenze future e considerazioni emergenti
Il panorama delle minacce persistenti avanzate sta entrando in un periodo di rapida trasformazione, guidato dall'adozione dell'intelligenza artificiale da entrambe le parti in causa. Nei prossimi 12-24 mesi, le organizzazioni dovrebbero prepararsi ad affrontare diversi sviluppi chiave.
Le operazioni APT basate sull'intelligenza artificiale (IA) sono destinate a crescere in modo esponenziale. Considerando che l'80% delle phishing utilizza già contenuti generati dall'IA e che APT36 ha dimostrato come l'IA possa fungere da catena malware , è prevedibile che un numero crescente di gruppi APT adotti l'IA per automatizzare le attività di ricognizione, personalizzare le tecniche di ingegneria sociale e malware polimorfico. Il 48% dei professionisti della sicurezza informatica che classifica l'IA agentica come il principale vettore di attacco per il 2026 sta rispondendo a una minaccia reale e immediata: gli agenti IA introducono nuove identità non umane che ampliano la superficie di attacco.
Gli attacchi mirati alle identità sono destinati a intensificarsi. Il passaggio da operazioni APT malware a quelle basate sulle identità sta accelerando. Man mano che le organizzazioni implementano un numero crescente di cloud , applicazioni SaaS e agenti di intelligenza artificiale, il numero di identità non umane — chiavi API, account di servizio, token OAuth — crescerà in modo esponenziale. I gruppi APT seguiranno queste identità.
I quadri normativi diventeranno più rigorosi. Si prevede che la norma NIST SP 800-172 Rev. 1 affronti i modelli di attacchi APT cloud e le minacce legate all'intelligenza artificiale. Il taglio di bilancio di 495 milioni di dollari proposto dalla CISA, se approvato, potrebbe ridurre la capacità di coordinamento nazionale per la difesa dagli attacchi APT proprio nel momento in cui è più necessaria. Le organizzazioni non dovrebbero fare affidamento esclusivamente sul coordinamento governativo e dovrebbero investire nelle proprie capacità di rilevamento e risposta.
I dispositivi perimetrali continueranno a rappresentare obiettivi di grande valore. Lo sfruttamento dei router e degli apparecchi VPN Salt Typhoon ha dimostrato che i dispositivi perimetrali di rete costituiscono punti di accesso iniziali molto appetibili. Le organizzazioni dovrebbero dare priorità alla visibilità a livello di rete e al monitoraggio dell'integrità del firmware per questi dispositivi.
Conclusione
Le minacce persistenti avanzate (APT) rappresentano la categoria più sofisticata di avversari informatici e le loro operazioni stanno subendo un'accelerazione. Con attacchi che passano dall'accesso all'esfiltrazione in appena 72 minuti, lo sfruttamento delle identità presente nel 90% delle indagini e tecniche operative potenziate dall'intelligenza artificiale che ampliano le operazioni APT a livello globale, i difensori si trovano ad affrontare una sfida radicalmente diversa rispetto a quella di appena due anni fa.
La risposta più efficace combina un sistema di rilevamento a più livelli che copre la rete, le identità, endpoint e cloud con attività proattive di ricerca delle minacce e l'utilizzo operativo delle informazioni sulle minacce. Nessuno strumento è sufficiente da solo. Le organizzazioni dovrebbero allineare le proprie difese a framework consolidati come NIST SP 800-172 e MITRE ATT&CK, investire in capacità di rilevamento comportamentale in grado di identificare i comportamenti post-compromissione indipendentemente dagli strumenti utilizzati dall'autore dell'attacco e preparare piani di risposta agli incidenti sia per operazioni furtive di lunga durata che per campagne di esfiltrazione rapida.
Le organizzazioni che partono dal presupposto che le violazioni possano verificarsi e sviluppano di conseguenza capacità di rilevamento — anziché affidarsi esclusivamente alla prevenzione — sono nella posizione migliore per individuare e bloccare gli operatori APT prima che raggiungano i loro obiettivi.
Domande frequenti
Qual è la differenza tra un APT e un normale attacco informatico?
Gli APT si differenziano dagli attacchi informatici convenzionali per tre aspetti fondamentali. In primo luogo, sono condotti da attori malintenzionati dotati di ingenti risorse, solitamente sostenuti da Stati, che perseguono obiettivi strategici specifici quali lo spionaggio, il furto di proprietà intellettuale o il sabotaggio — e non un guadagno economico opportunistico. In secondo luogo, gli APT garantiscono una persistenza a lungo termine, misurabile in mesi o anni. Il tempo medio di permanenza di un APT è di 95 giorni, e campagne come Salt Typhoon per uno o due anni prima di essere scoperte. In terzo luogo, gli APT utilizzano metodologie di attacco sofisticate e in più fasi che si adattano in tempo reale per eludere il rilevamento. Mentre un tipico attacco informatico potrebbe distribuire malware di uso comune malware passare oltre, gli operatori APT prendono decisioni guidate dall'uomo, cambiano strategia in base a ciò che scoprono e adattano le loro tecniche per aggirare le difese specifiche che incontrano. Questa sofisticazione richiede approcci di rilevamento altrettanto sofisticati, in particolare l'analisi comportamentale e il monitoraggio dell'identità.
Gli attacchi APT hanno ripercussioni sulla gente comune?
Sebbene gli APT prendano di mira principalmente governi, infrastrutture critiche e grandi imprese, spesso anche i singoli cittadini ne subiscono le conseguenze indirettamente. Quando Salt Typhoon nove operatori di telecomunicazioni statunitensi e i sistemi di intercettazione CALEA, ha avuto accesso ai metadati delle comunicazioni di milioni di utenti comuni. Le violazioni della catena di approvvigionamento — come l’attacco del Gruppo Lazarus all’ambiente di sviluppo di Safe{Wallet} — possono propagarsi a cascata a valle, colpendo i singoli consumatori. I dati personali rubati nelle campagne di spionaggio APT possono anche essere riutilizzati per successive operazioni di furto d'identità. Inoltre, quando gli APT prendono di mira le infrastrutture energetiche con attacchi wiper, come ha fatto Sandworm contro i sistemi ucraini e polacchi, l'interruzione colpisce direttamente la popolazione civile.
Quanto durano in genere gli attacchi APT?
I tempi di permanenza delle APT — ovvero il periodo che intercorre tra la compromissione iniziale e il rilevamento — sono in media di 95 giorni, con alcune campagne che si protraggono per oltre un anno. La campagna Salt Typhoon è rimasta attiva per uno o due anni prima di essere scoperta. Ciò contrasta nettamente con il tempo mediano di permanenza degli attacchi informatici in generale, pari a circa otto giorni. Tuttavia, le operazioni APT più rapide stanno accelerando in modo drammatico. La ricerca condotta da Unit 42 nel 2026 mostra che le campagne più veloci passano ora dall'accesso iniziale all'esfiltrazione dei dati in soli 72 minuti, quattro volte più velocemente rispetto all'anno precedente. Ciò significa che i difensori devono affrontare una doppia sfida: rilevare operazioni furtive di lunga durata e rispondere a campagne "smash-and-grab" eseguite rapidamente, entrambe condotte da avversari sofisticati.
Qual è la differenza tra un APT e un ransomware?
Gli APT tradizionali conducono attività di spionaggio, sabotaggio o furto strategico per lunghi periodi, puntando sulla discrezione, mentre il ransomware privilegia la crittografia rapida e l’estorsione a scopo di lucro. Tuttavia, questa distinzione sta diventando sempre meno netta. Il Gruppo Lazarus opera sia per lo spionaggio che per il furto finanziario: la sua rapina da 1,5 miliardi di dollari ai danni di Bybit sembra più un atto di criminalità informatica che di spionaggio. Alcuni gruppi di ransomware utilizzano ora tecniche di livello APT, tra cui ricognizione estesa, strumenti personalizzati e tecniche "living-off-the-land". Le organizzazioni criminali ben finanziate assomigliano sempre più agli APT sponsorizzati dallo Stato per sofisticazione, pazienza e sicurezza operativa. Per i difensori, l'implicazione pratica è che le stesse capacità di rilevamento comportamentale necessarie per la difesa dagli APT — monitoraggio dei movimenti laterali, abuso delle credenziali e staging dei dati — proteggono anche dalle sofisticate operazioni di ransomware.
Quali sono i settori più presi di mira dagli attacchi APT?
I settori più presi di mira nel 2025 e nel 2026 includono le telecomunicazioni (Salt Typhoon, UNC3886), la pubblica amministrazione e la diplomazia (Silver Dragon, TGR-STA-1030), il settore della difesa (numerose campagne APT provenienti dalla Repubblica Popolare Cinese e dalla Russia), l’energia e le infrastrutture critiche (Sandworm), nonché i servizi finanziari e le criptovalute (Lazarus Group). La Cina e la Corea del Nord rappresentano il 55% degli attacchi APT globali. L'ENISA ha documentato 4.875 incidenti nella sola UE da luglio 2024 a giugno 2025. Il settore delle telecomunicazioni è stato oggetto di attacchi particolarmente intensi perché l'accesso alle infrastrutture di telecomunicazione fornisce alle agenzie di intelligence capacità di sorveglianza su milioni di utenti, come ha dimostrato la compromissione delle intercettazioni telefoniche Salt Typhoon da parte di Salt Typhoon .
Quanto costano alle organizzazioni gli attacchi APT?
I costi variano notevolmente a seconda della portata e degli obiettivi della campagna. L'attacco sferrato dal Lazarus Group contro Bybit ha causato una perdita di 1,5 miliardi di dollari in un unico episodio: il più ingente impatto finanziario mai registrato in un attacco APT. Oltre al furto diretto, le intrusioni APT generano costi legati alle indagini, alla risoluzione dei problemi, alle sanzioni normative, all'interruzione dell'attività e al danno reputazionale, che possono ammontare a milioni di dollari per singolo incidente. Il mercato della protezione APT, valutato a circa 9,2 miliardi di dollari nel 2025 e in crescita con un CAGR del 19,9%, riflette l'entità degli investimenti delle organizzazioni nella difesa. Per la maggior parte delle organizzazioni, il costo di un APT non rilevato che opera all'interno del loro ambiente per mesi supera di gran lunga il costo dell'implementazione di solide funzionalità di rilevamento comportamentale, monitoraggio delle identità e sicurezza di rete.
Il termine "APT" è ancora appropriato?
La definizione è in continua evoluzione. La definizione originale del NIST si riferisce esclusivamente ad attori statali o sponsorizzati dallo Stato. Tuttavia, il panorama delle minacce è cambiato. Gruppi di criminali informatici ben finanziati utilizzano ormai tecniche di livello APT, tra cui malware personalizzato, ricognizione approfondita e operazioni in più fasi. Gruppi come il Lazarus Group operano sia per scopi di spionaggio che per obiettivi finanziari, rendendo meno netta la linea di demarcazione tra operazioni sponsorizzate dallo Stato e criminalità informatica. Il settore utilizza sempre più spesso il termine "APT" per descrivere qualsiasi attore di minaccia persistente e sofisticato con risorse sostanziali, indipendentemente dal fatto che sia strettamente sponsorizzato dallo Stato. Per i difensori, la distinzione conta meno della realtà: che un avversario sia un servizio di intelligence di uno Stato-nazione o un'organizzazione criminale ben finanziata, i requisiti di rilevamento e risposta sono fondamentalmente gli stessi.