Once attackers get in, they don’t leave.
Security discussions often focus on the moment an attacker breaks in. That moment matters, but it rarely defines the outcome of the intrusion.
What determines whether an incident becomes a breach is persistence.
Persistence is how attackers stay inside your environment after gaining access. It allows them to return even after being removed, maintain long-term control, and quietly explore the network for valuable systems and data.
In modern hybrid environments, persistence is often more dangerous than the initial compromise itself.
Attackers don’t need to break in again if they never truly left.
Why Persistence Is Easier in Hybrid Networks
The modern enterprise network is no longer a single environment. It spans:
- on-premises infrastructure
- cloud workloads
- Piattaforme SaaS
- remote devices
- identity platforms
Each of these layers provides opportunities for attackers to hide activity and maintain control.
Hybrid networks also introduce gaps between tools. Endpoint detection may only monitor managed devices. IAM platforms see authentication events but not what happens afterward. Cloud tools monitor configuration, not runtime behavior.
Attackers exploit these blind spots.
Once inside, their goal is simple: establish a foothold that survives disruption.
This is persistence.
Real-World Techniques Attackers Use for Persistence
Persistence rarely relies on a single method. Attackers often combine several techniques so that if one access point is removed, another remains. Below are the most common approaches used by attackers.
1. Backdoors and Hidden Remote Access
One common tactic is installing a backdoor, software that allows remote access to a compromised system while appearing legitimate.
Some attackers deploy hidden remote desktop environments using tools like Hidden VNC (hVNC). These create invisible desktop sessions that only the attacker can see.
The victim continues working normally while the attacker controls a separate hidden environment on the same machine.
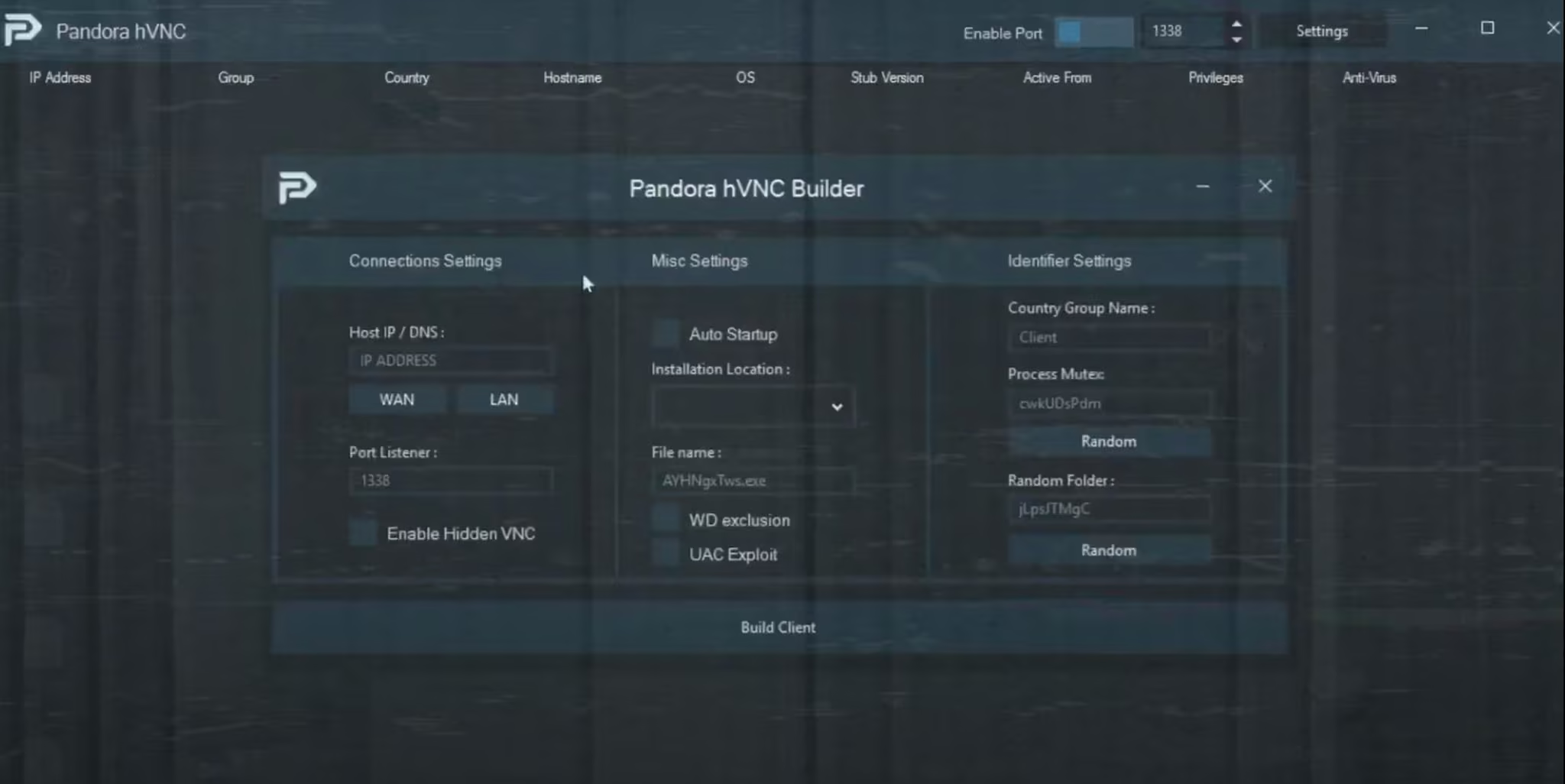
Other backdoors operate as lightweight proxies or remote shells. These tools quietly relay traffic between the attacker and internal systems, turning the compromised machine into a permanent access point inside the network. Once installed, these tools often restart automatically after system reboots.
2. Persistent Network Tunnels
Instead of maintaining a traditional remote shell, attackers frequently create persistent tunnels. Tools such as reverse SOCKS proxies or fast reverse proxies allow the attacker to route traffic through the compromised system and access internal resources remotely.
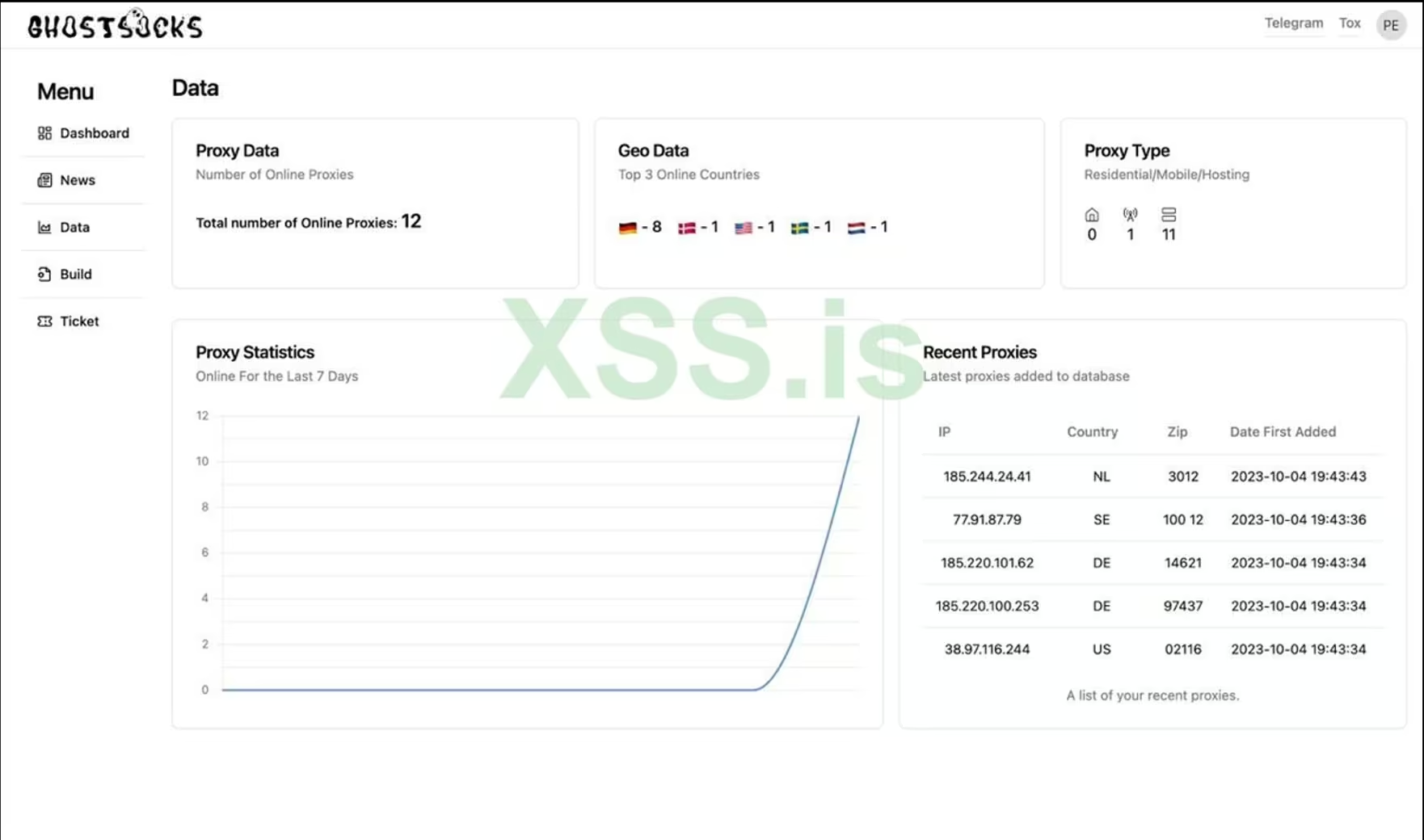
This technique effectively transforms a compromised host into a stepping stone inside the network.
From the defender’s perspective, traffic may appear to be normal outbound HTTPS communication.
From the attacker’s perspective, it becomes a stable internal pivot point.
3. Command-and-Control Beacons
Many intrusion frameworks rely on beacons that periodically contact attacker infrastructure.
Tools such as Cobalt Strike or Brute Ratel deploy small agents that “check in” at regular intervals to receive commands. These agents can:
- execute commands remotely
- download additional payloads
- reinstall persistence mechanisms if removed
- coordinate lateral movement across the network
Because these beacons communicate intermittently and often use encrypted channels, they blend easily into normal network traffic.
4. Token Abuse and Identity Persistence
Persistence doesn’t always involve malware.
In many cases, attackers simply exploit the way authentication systems work.
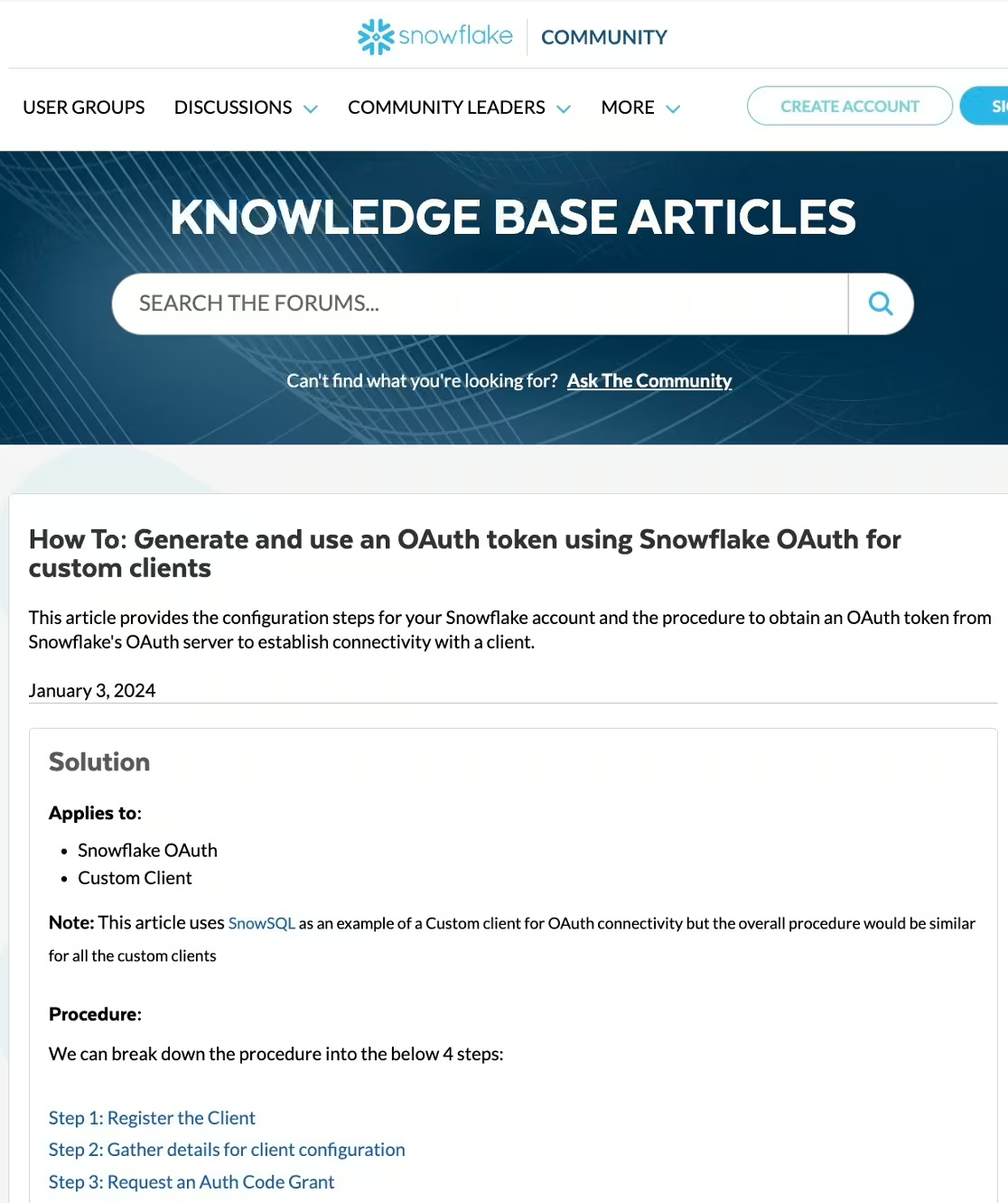
For example, cloud services often rely on tokens to maintain authenticated sessions. These tokens can allow users or applications to reconnect without logging in again.
In the Snowflake supply-chain compromise, attackers leveraged authentication tokens that allowed them to maintain access even after defenders believed the intrusion had been removed.
If attackers possess long-lived tokens or the ability to generate new ones, they can quietly regain access without triggering traditional login alerts.
"I can still run commands because I have the ‘masterToken’ for every account."
Ellyel8 – the attacker behind the Snowflake Breach*
5. Living Off the Land
Many sophisticated attackers avoid installing obvious malware altogether.
Instead, they rely on tools already built into the operating system.
This technique, known as living off the land, uses legitimate administrative tools such as:
- PowerShell
- Windows Management Instrumentation (WMI)
- scheduled tasks
These tools allow attackers to execute commands, gather system information, and schedule recurring activity that survives system restarts.
From a defender’s perspective, these actions often resemble routine administrative activity. That ambiguity is precisely why attackers prefer them.
Why Prevention Tools Miss Persistence
Preventive controls remain essential. MFA, EDR, and vulnerability management all reduce the chances of an initial compromise.
But persistence often operates outside their visibility.
Attackers commonly exploit several limitations:
- Attackers operate from unmanaged or trusted endpoints where EDR isn’t installed.
- Traffic is tunneled through encrypted DNS or HTTPS sessions that appear legitimate.
- Logs are deleted before SIEM platforms ingest them.
- Administrative tools generate activity that looks identical to normal operations.
When legitimate credentials and built-in tools are involved, prevention alone cannot reliably distinguish attackers from administrators.
Detection must focus on behavior.
Detecting Persistence Before It Becomes a Breach
Persistence leaves patterns. Even stealthy attackers generate signals across identity systems, network traffic, and cloud activity.
SOC teams should look for behaviors such as:
- unusual outbound tunnels or proxy connections
- command-and-control beacon patterns
- abnormal token usage or session activity
- administrative commands executed from unexpected systems
- identity behavior inconsistent with historical activity
Detecting persistence requires visibility across environments.
How the Vectra AI Platform Reveals Hidden Footholds
Persistence mechanisms are designed to survive cleanup efforts. Backdoors restart after reboots, authentication tokens renew sessions automatically, and command-and-control channels blend into normal encrypted traffic.
Many of these techniques operate outside endpoint visibility.
The Vectra AI Platform detects persistence by observing the behaviors attackers cannot easily conceal. Network communications, identity interactions, and command patterns reveal when compromised systems maintain contact with external infrastructure or when identities begin behaving in ways inconsistent with normal operations.
Because detection happens at the network and identity layers, attackers cannot disable this visibility by stopping agents or clearing local logs. Persistent tunnels, beacon traffic, and abnormal identity activity still generate signals that expose the foothold.
For SOC teams, this provides a reliable way to identify attackers who believe they are already hidden.
I tuoi prossimi passi
Once attackers gain access, their priority shifts from entry to survival.
Persistence techniques allow them to stay inside the environment even after partial remediation. Backdoors, command-and-control channels, authentication tokens, and scheduled tasks all help attackers quietly maintain control.
In Attack Lab Episode 2: Persistence – How attackers hide in the network, we break down how real attackers establish these footholds and why many traditional security tools struggle to detect them.
If you're curious about what they do next, watch Episode 3: Lateral Movement - How attackers move through the network.
---
*Citazione dal libro di Vinny Troia "Grey Area: Dark Web Data Collection and the Future of OSINT" (Area grigia: raccolta dati dal dark web e il futuro dell'OSINT)

