What is OPSEC? Operational Security Explained
Approfondimenti chiave
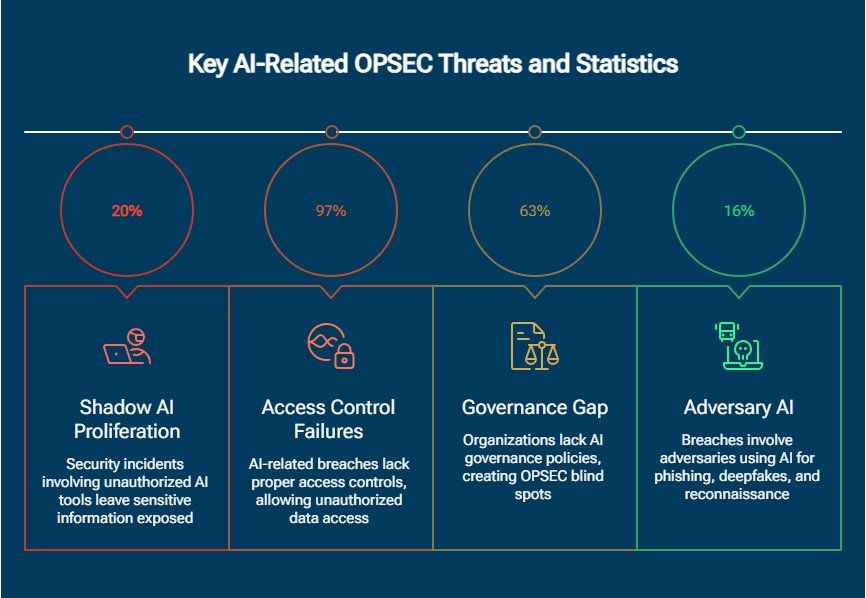
- 13% of all data breaches now involve AI models, applications, or infrastructure — with 97% of these incidents lacking proper access controls (IBM Cost of a Data Breach Report 2025)
- Shadow AI accounts for 20% of security incidents and adds an average of $670,000 to breach costs beyond baseline (IBM Cost of a Data Breach Report 2025)
- 63% of organizations either lack AI governance policies or are still developing them while actively deploying AI capabilities (IBM Cost of a Data Breach Report 2025)
- CMMC 2.0 (effective November 10, 2025) mandates comprehensive OPSEC programs for all federal contractors, requiring compliance with NIST SP 800-171 Rev 2 (CMMC Model Documentation, U.S. Department of Defense)
Operational security (OPSEC) is a systematic, five-step process that protects sensitive information by analyzing operations from an adversary's perspective. It identifies what data requires protection, evaluates potential threats and vulnerabilities, and implements targeted countermeasures before adversaries can exploit exposed information.
Che cos'è l'OPSEC (sicurezza delle operazioni)?
OPSEC (operations security) is a systematic process designed to identify, analyze, and protect critical information that adversaries could exploit to harm an organization's operations, personnel, or strategic objectives. It examines friendly activities from an adversary's perspective, analyzing operations as an attacker would, to identify vulnerabilities and implement countermeasures that deny adversaries the information needed to plan and execute attacks.
The process originated during the Vietnam War when the U.S. military formed the Purple Dragon team in 1966 to investigate why enemy forces consistently anticipated American operations. The team discovered that seemingly innocuous information, when aggregated, revealed operational patterns adversaries exploited without requiring access to classified data. This led to the five-step OPSEC methodology that remains the foundation of modern operational security practice.
Modern OPSEC encompasses protecting any information that could provide adversaries with operational advantages: technical configurations, business processes, personnel information, and strategic plans that collectively form an organization's attack surface.
Why OPSEC matters for enterprise security
The cost of OPSEC failure is measurable and rising:
- Global average data breach cost: $4.44 million (2025); U.S. organizations: $10.22 million per incident
- Organizations with mature OPSEC programs experience 71% fewer security incidents
- AI-powered defenses reduce breach lifecycles by up to 80 days
- Phishing accounts for 16% of all breaches at an average cost of $4.80 million per incident
Unlike reactive security measures that respond to attacks in progress, OPSEC prevents security hackers and threat actors from gathering the intelligence needed to launch targeted attacks. Organizations with mature OPSEC programs report improved regulatory compliance, reduced insurance premiums, and enhanced customer trust alongside direct cost reduction.
The emergence of shadow AI has introduced a new class of OPSEC vulnerabilities, covered in depth in the AI-related OPSEC challenges section below.
Operational security in enterprise contexts: While OPSEC originated in military doctrine, operational security has become a core discipline for enterprise security teams, encompassing the protection of business processes, M&A activities, supply chain relationships, and cloud infrastructure from adversarial reconnaissance.
I 5 passaggi dell'OPSEC
The five-step OPSEC process provides a systematic framework for protecting critical information from adversary exploitation. This proven methodology creates a repeatable process organizations can adapt to their specific threat landscapes and operational requirements.
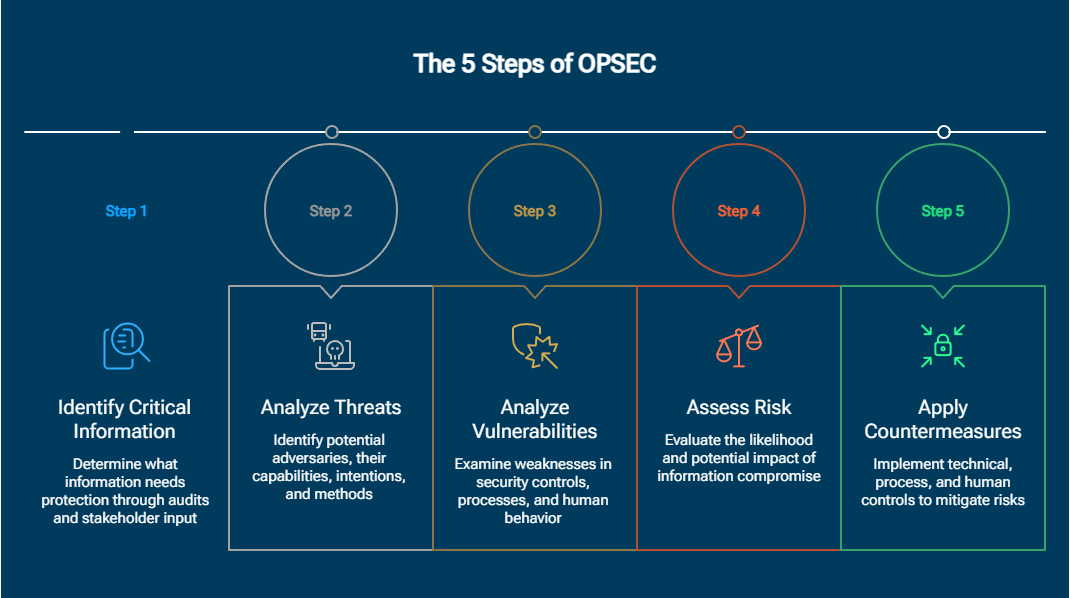
Fase 1 — Identificare le informazioni critiche
Organizations must determine what information requires protection by conducting comprehensive audits of data, systems, and operations. Critical information extends beyond obvious targets like intellectual property and financial data to include merger plans, infrastructure configurations, employee directories, and strategic initiatives adversaries could exploit.
Effective identification requires input from stakeholders across the organization, as critical information varies by department and function. Security teams should work with business units to catalog information assets, classify sensitivity levels, and understand operational importance, ensuring comprehensive coverage while avoiding over-classification that dilutes protection efforts.
Modern enterprises must also account for digital breadcrumbs that reveal critical information indirectly: API endpoints, DNS records, certificate transparency logs, and cloud storage buckets that expose organizational structures and technologies facilitating targeted attacks.
Fase 2 — Analizzare le minacce
Threat analysis identifies potential adversaries, their capabilities, intentions, and methods of operation. Understanding how adversaries progress through the cyber kill chain, from initial intelligence gathering through exploitation and exfiltration, helps security teams determine which information assets require the most stringent OPSEC protection at each stage.
Each threat actor employs different tactics, techniques, and procedures (TTPs). Nation-state actors possess advanced persistent threat capabilities and zero-day exploits, while cybercriminals leverage ransomware-as-a-service platforms and social engineering. Competitor threats focus on intellectual property theft and strategic intelligence gathering through both technical and human intelligence methods.
Fase 3 — Analizzare le vulnerabilità
Vulnerability analysis examines how adversaries could obtain critical information through weaknesses in security controls, processes, or human behavior, thinking like an attacker to identify exploitable gaps that traditional security assessments overlook.
Common vulnerabilities include social media oversharing, predictable operational patterns that reveal timing and locations, unsecured communications channels, and inadequate access controls. Supply chain relationships create additional exposure when partners lack equivalent security standards. Cloud environments introduce shared responsibility gaps, multi-tenancy risks, and API exposures that require explicit OPSEC assessment alongside traditional controls.
Fase 4 — Valutare il rischio
Risk assessment evaluates the likelihood and potential impact of critical information compromise by combining threat and vulnerability analyses, prioritizing protection efforts based on business criticality, regulatory requirements, and available resources.
Quantitative methodologies assign numerical values to probability and impact, enabling data-driven countermeasure investment decisions. Qualitative assessments provide contextual understanding of risks that resist quantification, reputational damage, competitive disadvantage, or cascading compromises where one breach enables additional attacks.
Fase 5 — Applicare le contromisure
Countermeasures eliminate or reduce vulnerabilities through technical controls, process improvements, and awareness training, balancing security with operational efficiency.
Technical countermeasures include encryption, access restrictions, network segmentation, and anomalous behavior monitoring. Process countermeasures establish need-to-know policies, information handling procedures, and incident response protocols. Human countermeasures focus on security awareness training and creating security-conscious cultures.
Organizations should pilot countermeasures in controlled environments, measure their effectiveness, and adjust based on real-world results.
OPSEC vs InfoSec: comprendere la differenza
OPSEC focuses specifically on protecting critical operational information from adversarial exploitation. InfoSec implements comprehensive technical controls to secure all information systems and data.
The comparison below highlights how these two approaches differ across focus, methodology, and scope.
The key distinction is perspective: OPSEC identifies what information controls must protect and how adversaries might circumvent them; InfoSec provides the technical capabilities to protect it. Organizations achieve optimal security by integrating both disciplines.
What is OPSEC liability?
OPSEC liability is the organizational exposure created when uncontrolled information disclosure gives adversaries the intelligence required to plan and execute targeted attacks. Unlike a technical vulnerability, a flaw in a system, OPSEC liability accumulates through the aggregation of seemingly harmless information into actionable intelligence.
Individual pieces of publicly available information are individually innocuous. A job posting reveals a technology stack. A LinkedIn profile lists project responsibilities. A press release announces a strategic partnership. A conference presentation describes internal security architecture. Aggregated, these disclosures create a detailed intelligence picture adversaries use to identify high-value targets, map organizational structures, and time attacks for maximum impact.
Adversaries conducting reconnaissance use data aggregation to reconstruct an organization's attack surface from public sources without accessing a single protected system, combining job postings, LinkedIn profiles, partner announcements, and DNS records into a detailed intelligence picture that directs targeted attacks.
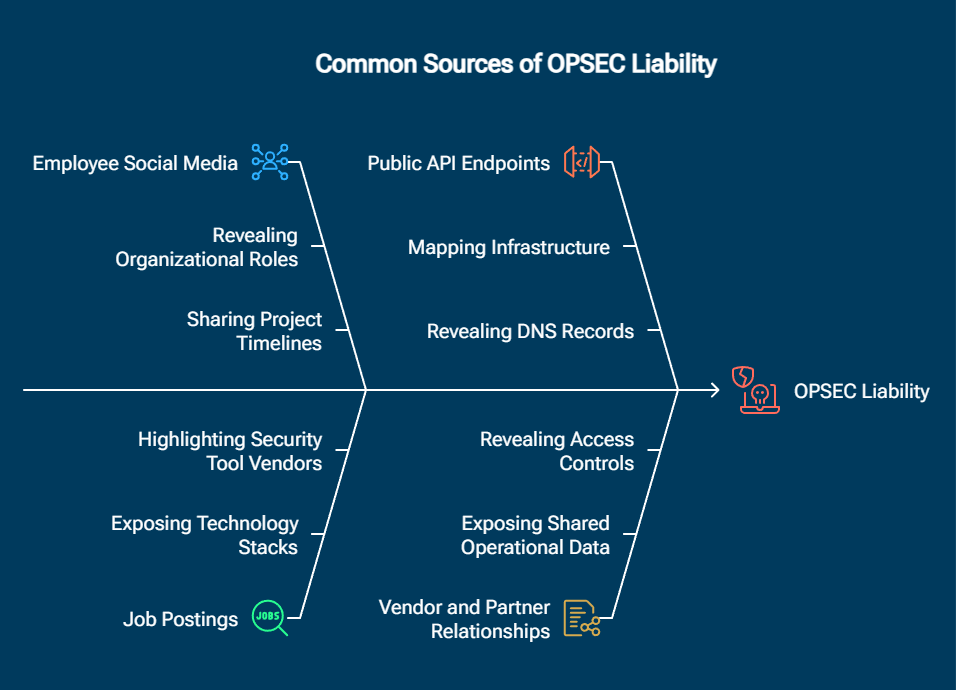
Common sources of OPSEC liability:
- Employee social media activity revealing organizational roles, locations, and project timelines
- Job postings exposing technology stacks, security tool vendors, and operational gaps
- Public API endpoints, DNS records, and certificate transparency logs that map infrastructure
- Vendor and partner relationships exposing shared operational data and access controls
- Conference presentations, press releases, and earnings calls that telegraph strategic initiatives
Reducing OPSEC liability requires regular open-source intelligence (OSINT) audits examining what adversaries can aggregate from public sources before any security alert triggers.
Esempi e casi d'uso di OPSEC
Recent incidents demonstrate how OPSEC failures in communication platforms, cloud configurations, and third-party relationships create cascading compromises.
Cronologia degli incidenti OPSEC nel 2025
The timeline below outlines real-world OPSEC failures in 2025, showing how each incident unfolded, what caused it, and the practical lessons organizations can apply to prevent similar exposures.
Migliori pratiche OPSEC
Implementing effective OPSEC requires addressing technical controls, organizational processes, and human factors simultaneously.
Implement least-privilege access controls based on zero-trust principles that verify every request regardless of source, preventing lateral movement if adversaries compromise individual accounts. Regular access reviews ensure permissions align with current job responsibilities.
Conduct quarterly OPSEC assessments using the five-step process to identify emerging vulnerabilities and verify countermeasure effectiveness. External red team exercises provide adversarial perspectives that internal teams miss due to organizational blind spots.
Compartmentalization limits information exposure by ensuring individuals only access data necessary for their specific functions. Dedicated communication channels and restricted documentation repositories prevent single compromises from exposing entire operations.
Technical monitoring, SIEM systems, user and entity behavior analytics (UEBA), and endpoint detection and response (EDR), must detect anomalous behavior indicating reconnaissance: unusual access patterns, data aggregation attempts, and privilege escalation. EDR extends OPSEC controls by monitoring device-level behavior for signs that adversaries are acting on gathered intelligence, even when they use legitimate tools and valid credentials.
Lista di controllo per l'implementazione dell'OPSEC
- Stabilire politiche di classificazione delle informazioni che definiscano i livelli di sensibilità e i requisiti di trattamento.
- Deploy multi-factor authentication for all systems accessing critical information
- Implementare strumenti di prevenzione della perdita di dati che monitorino i trasferimenti non autorizzati di informazioni.
- Creare programmi di formazione per i dipendenti che trattino i rischi legati al social engineering, phishing e ai social media.
- Sviluppare procedure di risposta agli incidenti che affrontino specificamente le violazioni delle informazioni.
- Monitorare i forum del dark web e i siti di paste per individuare eventuali fughe di informazioni relative all'organizzazione.
- Effettuare valutazioni periodiche della vulnerabilità delle risorse e delle API accessibili al pubblico.
- Stabilire canali di comunicazione sicuri per discutere operazioni sensibili
- Implementare politiche di governance dell'IA con processi di approvazione chiari per l'utilizzo degli strumenti di IA.
- Verifica regolare delle implementazioni di IA ombra e dell'utilizzo non autorizzato dei servizi di IA
- Stabilire controlli di accesso per modelli di IA, applicazioni e dati di addestramento
- Monitorare la sicurezza della catena di fornitura dell'IA, inclusi API, plug-in e modelli di terze parti.
Sfide OPSEC relative all'intelligenza artificiale
The rapid adoption of artificial intelligence has created a new frontier for OPSEC vulnerabilities. IBM's 2025 Data Breach Report identifies AI and shadow AI as emerging critical risks, with 13% of all data breaches now involving AI models, applications, or infrastructure, a category that barely existed in previous years.
Diffusione dell'intelligenza artificiale ombra
When employees use unauthorized AI tools without employer approval, they create unmonitored channels for sensitive information to leave organizational boundaries. 20% of security incidents involve shadow AI, adding an average of $670,000 to breach costs. These deployments bypass security controls, lack data governance oversight, and create audit gaps adversaries exploit, employees uploading proprietary code, customer data, or strategic plans to external AI services inadvertently expose this information to third parties with unknown security postures.
Errori nel controllo degli accessi tramite IA
97% of AI-related breaches lack proper access controls. Organizations deploying AI models fail to implement basic security hygiene, authentication requirements, authorization checks, input validation, and audit logging, creating scenarios where attackers can query AI systems for sensitive information, manipulate outputs, or exfiltrate training data without detection. Unlike traditional applications, AI models can inadvertently memorize and regurgitate sensitive training data, respond to adversarial prompts that bypass intended restrictions, and serve as aggregation points for information from multiple sources.
Divario nella governance dell'IA
63% of organizations lack AI governance policies or are still developing them while actively deploying AI capabilities, creating OPSEC blind spots where critical information flows through AI systems without oversight. Effective AI governance requires policies covering: acceptable use of approved and unauthorized AI tools, data classification requirements for AI interactions, approval processes for new AI deployments, monitoring and audit procedures, and incident response plans for AI-related compromises.
Uso ostile dell'IA
16% of breaches involved adversaries using AI technologies, with 37% using AI-generated phishing communications to enable account takeover and 35% deploying deepfakes for impersonation. Adversaries use AI for automated reconnaissance from public sources, generating social engineering pretexts, running SEO poisoning campaigns that surface malicious download pages through manipulated search results, and adapting attack strategies in real-time based on defender responses.
How Vectra AI addresses AI-related OPSEC failures
Vectra AI approaches OPSEC through Attack Signal Intelligence™, detecting behavioral patterns that indicate adversary reconnaissance and information-gathering activities before they escalate. By analyzing network traffic, identity behaviors, and cloud activities simultaneously, the platform exposes OPSEC failures manifesting as unusual access patterns, suspicious data movements, or privilege escalations that precede actual attacks, transforming OPSEC from a preventive checklist into a continuous detection capability that adapts as adversary techniques evolve.
Errori comuni nell'OPSEC e come evitarli
The four most common OPSEC failure patterns from 2025:
- Communication platform misconfiguration: The Signalgate leak exposed CIA identities through a single incorrectly added group member
- Development environment exposure: The F5 Networks breach compromised source code repositories lacking production-equivalent security controls
- Third-party platform risk: The Qantas/Salesforce breach exposed 5.7 million records across 39 companies through a single shared platform compromise
- Delayed patching: Oracle EBS zero-day exploitation succeeded because organizations failed to apply an available patch before Cl0p ransomware operators moved
Human error remains the primary OPSEC vulnerability. The psychological dimension of OPSEC, how adversaries exploit predictable human behavior patterns, is the hardest vulnerability to control through technical means alone. Social media oversharing reveals organizational structures, project timelines, and technology stacks that adversaries aggregate for reconnaissance. Phishing attacks succeed when employees lack awareness of social engineering techniques or feel pressured to respond quickly.
Prevenire i fallimenti OPSEC
Regular security assessments should examine not just traditional IT infrastructure but also collaboration platforms, development environments, and third-party relationships. Managed detection and response (MDR) services extend OPSEC effectiveness by providing 24/7 monitoring that detects when adversaries act on gathered intelligence, including during nights, weekends, and holidays when internal teams are least available to respond.
Organizations building an effective OPSEC program should prioritize the following controls, each addressing a common gap where reconnaissance activity converts into operational compromise:
- Behavioral monitoring and anomaly detection for insider threat activity
- Zero-trust access reviews covering terminated employees and role changes
- Vendor contracts specifying OPSEC requirements with audit rights
- Collaboration platform security audits covering cross-tenant sharing configurations
- Automated scanning of public-facing assets before each assessment cycle
Sources and Methodology
This guide draws on primary research reports, government documentation, and verified incident records current as of Q1 2026. All statistics reference their primary source. Where secondary sources reference primary research, the primary source is cited directly.
- IBM Cost of a Data Breach Report 2025 (ibm.com/reports/data-breach) — Source for breach cost figures, AI-related breach statistics, shadow AI incident rates, phishing cost data, and adversary AI adoption rates. IBM conducts this research annually in partnership with the Ponemon Institute across 604 organizations in 17 industries and 16 countries.
- CMMC Model Documentation — U.S. Department of Defense (dodcio.defense.gov/CMMC/Model) — Source for CMMC 2.0 effective date, Level 2 OPSEC requirements, and NIST SP 800-171 Rev 2 control alignment.
- NIST Special Publication 800-53 Rev 5 (csrc.nist.gov/publications/detail/sp/800-53/rev-5/final) — Source for SC-38 Operations Security control family and OPSEC control framework mapping.
- MITRE ATT&CK Framework (attack.mitre.org) — Source for adversary TTP references, reconnaissance technique mapping (T1595 Active Scanning, T1598 Phishing for Information), and threat actor behavior classification.
- CISA Emergency Directive 26-01 (cisa.gov/emergency-directive-26-01) — Source for F5 Networks nation-state breach documentation and remediation requirements.
- National OPSEC Program — U.S. Office of the Director of National Intelligence (dni.gov/index.php/ncsc-what-we-do/ncsc-protect-your-secrets/national-opsec-program) — Source for National OPSEC Awareness Month designation and government OPSEC program standards.
Incident Documentation
- Signalgate/Pentagon Signal leak (March 2025) — The Atlantic original reporting
- Qantas/Salesforce breach (October 2025) — Salesforce security advisory and Qantas official disclosure
- F5 Networks nation-state attack (October 2025) — CISA Emergency Directive 26-01 and F5 security advisory
- Oracle EBS CVE-2025-61882 (October 2025) — Oracle Critical Patch Update advisory and CISA KEV catalog
Domande frequenti
Cosa significa OPSEC?
OPSEC stands for operations security, a systematic process designed to identify, analyze, and protect critical information that adversaries could exploit. While the term originated in military intelligence, OPSEC applies broadly to any organization that must protect sensitive operational information from adversarial exploitation.
Qual è la prima legge dell'OPSEC?
The first law of OPSEC is: if you don't know the threat, how can you know what to protect? This principle establishes threat analysis as the foundation of all OPSEC activities. Organizations must identify specific adversaries, understand their capabilities and objectives, and evaluate what information those adversaries would find most valuable before implementing protective measures.
What is OPSEC liability?
OPSEC liability is the accumulated organizational exposure created when uncontrolled information disclosure provides adversaries with the intelligence to plan and execute targeted attacks. It arises from the aggregation of individually innocuous information, job postings, employee social profiles, partner announcements, and public infrastructure data, that adversaries combine into actionable intelligence. Reducing OPSEC liability requires continuous open-source exposure assessment alongside technical security controls.
In che modo l'OPSEC differisce dall'InfoSec?
OPSEC focuses on protecting critical operational information from adversarial exploitation by analyzing operations from an attacker's perspective. InfoSec implements comprehensive technical controls to secure all information systems and data. OPSEC identifies what information requires protection and how adversaries might obtain it; InfoSec provides the technical controls to protect it.
Quali settori hanno maggiormente bisogno dell'OPSEC?
All organizations benefit from OPSEC, but highest-risk industries include defense contractors and government agencies protecting classified information, financial services organizations securing transaction data, healthcare organizations protecting patient data, technology companies protecting intellectual property, and critical infrastructure operators protecting systems that could be targeted for disruption.
Con quale frequenza devono essere condotte le valutazioni OPSEC?
Formal OPSEC assessments should occur at least quarterly using the five-step process. Additional assessments should follow significant operational changes, new technology deployments, organizational restructuring, mergers and acquisitions, or security incidents. Continuous monitoring supplements periodic assessments to maintain real-time awareness of emerging vulnerabilities.
Quali sono gli errori più comuni in materia di OPSEC?
The most common OPSEC mistakes include oversharing on social media and professional networks, failing to assess third-party and supply chain risks, inadequate access controls, insufficient employee training on social engineering, delayed patching of known vulnerabilities, failure to monitor public-facing assets for information leakage, and lacking AI governance policies.
L'OPSEC si applica ai lavoratori remoti?
Yes, remote workers require specific OPSEC controls. Home networks lack enterprise security controls, creating vulnerabilities for sensitive communications and data access. Remote workers should use VPNs and encrypted communication tools, avoid sensitive discussions in public locations, and secure home networks with strong authentication. OPSEC requirements apply regardless of work location.