Mimikatz explained: the credential theft tool defenders must understand
Approfondimenti chiave
- Mimikatz remains a top threat in 2026. It ranked #4 in the Red Canary 2026 Threat Detection Report, affecting 3.1% of monitored customers, and is actively used by Play and Akira ransomware groups.
- Signature-based detection alone is no longer sufficient. Eighty-two percent of CrowdStrike detections in 2026 were malware-free, meaning attackers routinely bypass file-based signatures through PowerShell variants, renamed binaries, and in-memory execution.
- Layered defense is the only reliable strategy. Credential Guard, LSA Protection, WDigest hardening, and behavioral detection must work together — no single control stops all Mimikatz attack paths.
- Mimikatz maps to 17 MITRE ATT&CK techniques across four tactics. This makes it a critical tool to address for NIST CSF and CIS Controls compliance programs.
- Behavioral detection and ITDR are the future. Organizations that move beyond static rules to identity threat detection and response dramatically reduce mean time to detect credential theft.
Every credential in your environment is a potential skeleton key. Mimikatz — the open-source tool that has fueled credential theft for over a decade — remains one of the most dangerous post-exploitation tools in the wild. Over 50 advanced persistent threat groups use it, according to the MITRE ATT&CK Mimikatz entry (S0002). The 2025 Verizon DBIR found stolen credentials were the initial access vector in 22% of breaches. For defenders, understanding Mimikatz is not optional — it is essential.
What is Mimikatz?
Mimikatz is an open-source Windows credential extraction tool created by French security researcher Benjamin Delpy (gentilkiwi) in 2011 to demonstrate weaknesses in how Windows stores authentication credentials in memory. Originally a proof-of-concept, it quickly became one of the most widely adopted post-exploitation tools by both penetration testers and adversaries worldwide.
The name "Mimikatz" combines the French slang "mimi" (cute) with "katz" (cats) — a deceptively playful name for a tool that has enabled billions of dollars in damage. Mimikatz is not a virus or malware in the traditional sense. It is a dual-use security tool, classified by antivirus vendors as HackTool:Win32/Mimikatz because of how frequently threat actors abuse it. Possessing and using Mimikatz for authorized security testing is legal. Using it against systems without authorization violates computer fraud laws such as the CFAA in the United States and the Computer Misuse Act in the United Kingdom.
What makes Mimikatz significant is its scale of adoption. MITRE ATT&CK tracks over 50 threat groups that deploy Mimikatz as part of their operations. The Red Canary 2026 Threat Detection Report ranks it #4 among threats, affecting 3.1% of monitored customers even after excluding red team testing activity.
Why Mimikatz still matters in 2026
Despite being over 15 years old, Mimikatz is more relevant than ever. CISA advisories updated in June 2025 (Play ransomware) and November 2025 (Akira ransomware) confirm its active use in ongoing campaigns. The 2025 Verizon DBIR reports that 54% of ransomware victims had credentials previously exposed in infostealer logs — the exact type of credential material Mimikatz harvests. Benjamin Delpy continuously updates the tool to address new Windows security features, keeping it effective against modern operating systems including Windows 10 and Windows 11 when defenses are not properly configured.
How Mimikatz works
Mimikatz targets the Windows Local Security Authority Subsystem Service (LSASS) — the process responsible for enforcing security policies and handling user authentication. LSASS stores credential material in memory so users can access network resources without re-entering passwords. Mimikatz exploits this design by reading credential data directly from the LSASS process memory space.
To access LSASS memory, Mimikatz requires privilege escalation to administrator or SYSTEM-level access, specifically the SeDebugPrivilege token. Once elevated, the tool uses three primary modules:
- sekurlsa — Extracts credential material directly from LSASS process memory, including NTLM hashes, Kerberos tickets, and WDigest plaintext passwords
- lsadump — Reads credentials from the SAM database, LSA secrets, and Active Directory replication data (used in DCSync attacks)
- kerberos — Manipulates Kerberos tickets for golden ticket and silver ticket attacks
A particularly dangerous variant is Invoke-Mimikatz, a PowerShell script from the PowerSploit framework that runs Mimikatz entirely in memory without writing to disk. Red Canary's 2026 report identifies Invoke-Mimikatz with the -dumpcreds parameter as the most common execution method observed. This fileless approach bypasses file-based signature detection entirely, which is why defenders who rely solely on antivirus are at a significant disadvantage.
Credential types Mimikatz can extract
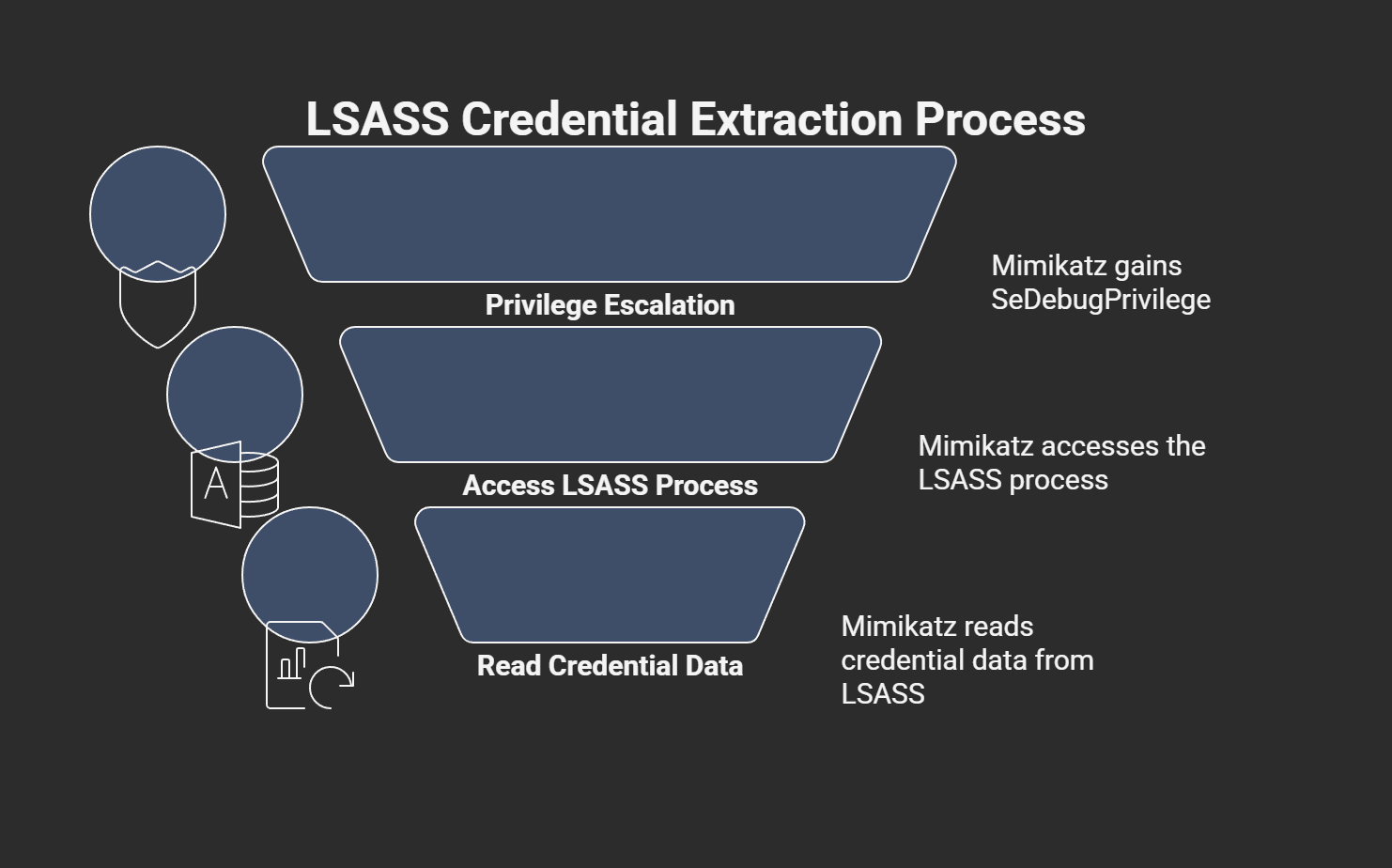
Table: Credential types Mimikatz can extract from Windows memory.
Mimikatz attack techniques
Mimikatz enables six major attack techniques spanning credential theft attacks, ticket forgery, and domain replication. Each maps to specific MITRE ATT&CK technique IDs with distinct detection indicators.
Table: Mimikatz attack techniques mapped to MITRE ATT&CK with detection indicators.
Pass-the-hash and pass-the-ticket
A pass-the-hash attack uses extracted NTLM hashes to authenticate to remote services without cracking the password. The attacker simply presents the hash directly to the authentication protocol. Pass-the-ticket works similarly but uses stolen Kerberos tickets instead of NTLM hashes. Both techniques enable lateral movement across the network and are particularly dangerous because they leave minimal forensic evidence compared to brute-force attacks.
Golden ticket and silver ticket attacks
A golden ticket attack is among the most devastating Mimikatz capabilities. By extracting the KRBTGT account hash — the key that encrypts all Kerberos ticket-granting tickets in Active Directory — an attacker can forge TGTs granting unrestricted domain access for any user, including non-existent ones. Golden tickets persist until the KRBTGT password is reset twice. Silver ticket attacks are more targeted, forging service-specific tickets using a service account hash. While silver tickets have a smaller blast radius, they are harder to detect because they bypass the domain controller entirely.
DCSync attacks
DCSync is a particularly dangerous Mimikatz technique (T1003.006) that impersonates a domain controller to request credential data through the Active Directory replication protocol. Unlike LSASS memory extraction, DCSync operates remotely — the attacker does not need to touch the target domain controller. It requires DS-Replication-Get-Changes privileges, which domain admins and domain controller accounts hold by default. Detection relies on monitoring Event ID 4662 for replication requests originating from non-domain-controller sources. Organizations using Kerberoasting detections often see DCSync as a natural escalation in the attack chain.
Mimikatz in practice: real-world attacks
Mimikatz has been central to some of the most destructive cyberattacks in history. According to the 2025 Verizon DBIR, 54% of ransomware victims had credentials previously exposed in infostealer logs, underscoring the real-world impact of credential theft tools.
- NotPetya (2017) — The most financially devastating cyberattack in history embedded a modified version of Mimikatz for credential extraction and lateral movement via WMIC and PsExec, causing $10 billion or more in damages globally.
- Play ransomware (2023-2025) — Approximately 900 organizations affected. Operators used LSASS dumping to minidump files followed by offline credential extraction. CISA advisory updated June 2025.
- Akira ransomware (2025) — Combined Kerberoasting with LSASS dumping and Mimikatz credential extraction in a chained attack sequence. CISA advisory updated November 2025.
- SLOW#TEMPEST (2024-2025) — Combined Cobalt Strike with Mimikatz pass-the-hash via RDP restrictedadmin mode, targeting organizations in East Asia.
- APT34/OilRig — The Iranian threat group deployed Mimikatz alongside LaZagne for credential dumping campaigns targeting Middle East energy sector infrastructure.
Each of these cases demonstrates a consistent pattern. Attackers gain initial access, escalate privileges, deploy Mimikatz or a variant to harvest credentials, and then move laterally across the environment. Disrupting any stage of this chain limits the blast radius.
Detecting and preventing Mimikatz
Effective Mimikatz defense requires layered controls combining LSASS access monitoring, behavioral threat detection, Credential Guard, and privilege reduction. No single solution stops all attack paths. Red Canary's 2026 report states that "the days of detecting LSASS-abusing tools like Mimikatz via traditional methods... are far behind us." Threat detection must evolve accordingly.
Detection engineering for Mimikatz
SOC teams should prioritize behavioral signals over static signatures. Here is a detection checklist organized by monitoring layer:
Table: Mimikatz detection checklist for SOC teams.
Proactive threat hunting for these indicators — rather than waiting for automated alerts — dramatically improves mean time to detect. The Splunk LSASS hunting guide and Red Canary LSASS Memory technique analysis provide additional detection engineering depth.
Hardening Windows against credential theft
Prevention controls reduce the attack surface before Mimikatz can execute:
- Enable Credential Guard — Uses virtualization-based security (VBS) to isolate credential material from LSASS. Microsoft recommends enabling Credential Guard with HVCI on all supported systems. Note that known bypass techniques exist (including NativeBypassCredGuard), which is why layered defense remains necessary.
- Enable LSA Protection (PPL) — Protected Process Light restricts which processes can access LSASS memory, blocking standard Mimikatz extraction.
- Disable WDigest authentication — Set the registry key
HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest\UseLogonCredentialto 0 to prevent cleartext password storage. - Implement least-privilege access — Reduce the number of accounts with administrator or domain admin privileges.
- Manage KRBTGT passwords — After suspected golden ticket compromise, perform a double-reset of the KRBTGT account password as part of incident response.
- Deploy endpoint detection — While Windows Defender detects known Mimikatz binaries (HackTool:Win32/Mimikatz), attackers routinely bypass signature-based detection through binary modification, custom compilation, and PowerShell variants.
Mimikatz, MITRE ATT&CK, and compliance
Mimikatz maps to 17 techniques across four MITRE ATT&CK tactics, making it one of the most broadly applicable tools in the framework (S0002). Organizations using compliance frameworks can map these techniques directly to control requirements.
Table: MITRE ATT&CK to NIST Cybersecurity Framework crosswalk for Mimikatz techniques.
These mappings align with NIST CSF controls PR.AC-1 (credential management), DE.CM-1 (network monitoring), and RS.AN-1 (investigation). CIS Controls v8 addresses Mimikatz risks through Controls 5 (Account Management), 6 (Access Control), 8 (Audit Logs), and 16 (Application Software Security).
Modern approaches to credential theft defense
The industry is shifting beyond signature-based Mimikatz detection toward behavioral and identity-centric approaches. CrowdStrike's 2026 Global Threat Report confirms that 82% of detections were malware-free, and AI-enabled adversary operations rose 89% year-over-year. Static rules simply cannot keep pace.
Network detection and response (NDR) provides visibility into lateral movement patterns that credential theft enables. Identity threat detection and response (ITDR) monitors authentication behavior across Active Directory and cloud identity providers to catch pass-the-hash, golden ticket, and DCSync attacks through behavioral anomalies rather than signatures.
How Vectra AI approaches credential theft detection
Vectra AI's Attack Signal Intelligence correlates identity-based attack signals across the modern network, detecting credential theft behaviors like pass-the-hash and golden ticket attacks through behavioral analysis rather than signatures. The platform provides coverage across on-premises Active Directory and cloud identity providers, enabling SOC teams to detect and respond to Mimikatz-style attacks in real time — reducing mean time to detect from hours to minutes.
Tendenze future e considerazioni emergenti
The credential theft landscape is evolving rapidly, with several developments set to reshape how organizations defend against Mimikatz and related tools over the next 12-24 months.
AI-powered credential attacks are accelerating. IBM X-Force's 2026 report found that over 300,000 ChatGPT credentials were stolen by infostealers, signaling that AI service accounts are becoming high-value targets alongside traditional Active Directory credentials. As organizations deploy more AI agents with privileged access, the attack surface for credential theft tools expands significantly.
Living-off-the-land credential dumping is growing. Attackers increasingly use built-in Windows tools like comsvcs.dll MiniDump and ProcDump (a legitimate Microsoft Sysinternals tool) to dump LSASS memory, avoiding the need to deploy Mimikatz at all. Defenders must monitor for the behavior — LSASS access patterns — not just the tool.
Third-party and supply chain credential exposure is doubling. The 2025 Verizon DBIR reports that breaches involving external partners doubled year-over-year to 30%. Credential theft tools deployed in partner environments can compromise interconnected organizations. This makes zero-trust architecture and continuous identity verification essential, not optional.
Regulatory pressure is increasing. Frameworks like NIST CSF 2.0 and evolving SEC disclosure requirements are pushing organizations to demonstrate specific credential protection controls and detection capabilities. Documenting MITRE ATT&CK coverage for tools like Mimikatz is becoming a compliance expectation, not just a best practice.
Organizations should prioritize investing in behavioral detection capabilities, ITDR platforms, and privileged access management to stay ahead of these trends.
Conclusione
Mimikatz has persisted as a dominant credential theft tool for over 15 years because it exploits fundamental design characteristics of Windows authentication. The credentials stored in LSASS memory — NTLM hashes, Kerberos tickets, and sometimes cleartext passwords — represent the keys to lateral movement, privilege escalation, and domain dominance.
Defending against Mimikatz requires a shift from signature-based detection to behavioral analysis. Monitor LSASS access patterns, enable Credential Guard and LSA Protection, disable WDigest, reduce privileged accounts, and invest in identity threat detection that catches the behavior — not just the binary. The organizations that fare best are those that assume compromise and focus on finding attackers who are already inside.
To explore how Attack Signal Intelligence detects credential theft behaviors across your hybrid environment, visit the Vectra AI platform or request a demo.
Domande frequenti
Is Mimikatz a virus?
No. Mimikatz is a legitimate open-source security tool, not malware in the traditional sense. However, antivirus vendors classify it as HackTool:Win32/Mimikatz because threat actors frequently abuse it during attacks. The distinction matters. Mimikatz does not self-replicate, does not install backdoors on its own, and does not spread autonomously. It is a dual-use tool with legitimate applications in authorized penetration testing and security research. That said, its presence on a system outside of authorized testing should be treated as a high-severity indicator of compromise. Security teams should configure endpoint detection to alert on any Mimikatz binary or in-memory execution, regardless of whether the specific variant is "known" malware. The dual-use nature means that context — who ran it, when, and with what authorization — determines whether it represents a threat.
Is Mimikatz illegal?
Mimikatz itself is legal to possess, download, and use in authorized security testing. The tool is freely available on GitHub and widely used by penetration testers, red teams, and security researchers worldwide. Legality depends entirely on authorization. Using Mimikatz against systems you own or have explicit written permission to test is legal in most jurisdictions. Using it against systems without authorization violates computer fraud laws including the Computer Fraud and Abuse Act (CFAA) in the United States, the Computer Misuse Act in the United Kingdom, and equivalent legislation in other countries. Many organizations include Mimikatz in their authorized security testing toolkits, and it is a standard component of frameworks like Metasploit and Cobalt Strike.
What is the difference between Mimikatz and Meterpreter?
Mimikatz is a standalone credential extraction tool focused specifically on Windows authentication — extracting NTLM hashes, Kerberos tickets, and cleartext passwords from memory. Meterpreter is a general-purpose post-exploitation payload within the Metasploit framework that provides remote access, file system manipulation, privilege escalation, and other capabilities. The two tools are complementary rather than competing. Mimikatz can be loaded as a module within Meterpreter (using the carico kiwi command), giving Metasploit operators access to Mimikatz credential extraction capabilities through the Meterpreter session. In practice, attackers often use Meterpreter for initial post-exploitation access and then load Mimikatz specifically when they need to harvest credentials for lateral movement.
Does Mimikatz work on Windows 10 and Windows 11?
Yes. Mimikatz is continuously updated by its author and works on modern Windows versions, including Windows 10 and Windows 11. However, Microsoft has significantly raised the bar with security features like Credential Guard, LSA Protection (PPL), and Hypervisor-Protected Code Integrity (HVCI). When these features are properly configured and enabled, they substantially limit Mimikatz effectiveness. The critical word is "properly configured." Many organizations have not enabled Credential Guard or LSA Protection, leaving their systems vulnerable to standard Mimikatz extraction techniques. Additionally, known bypass techniques exist even for Credential Guard deployments, which reinforces the need for layered defense rather than reliance on any single control.
What are alternatives to Mimikatz?
Several credential dumping tools serve similar functions with different detection profiles. LaZagne is a cross-platform, Python-based tool that extracts credentials from browsers, email clients, and operating system stores. Pypykatz is a pure Python implementation of Mimikatz that runs without compiling Windows-specific binaries. Dumpert uses direct system calls to dump LSASS memory, bypassing API-level monitoring hooks. ProcDump is a legitimate Microsoft Sysinternals tool frequently abused by attackers to create LSASS memory dumps. The comsvcs.dll MiniDump technique is a living-off-the-land approach using built-in Windows components. Each alternative has different OPSEC characteristics, and defenders must account for the full ecosystem of credential dumping tools — not just Mimikatz itself.
What is Invoke-Mimikatz?
Invoke-Mimikatz is a PowerShell script that is part of the PowerSploit framework. It executes Mimikatz entirely in memory without writing any files to disk, making it significantly harder to detect than the standalone executable. Red Canary's 2026 Threat Detection Report identifies Invoke-Mimikatz with the -dumpcreds parameter as the most common Mimikatz execution method observed in real-world attacks. Because it runs in memory, traditional file-based antivirus signatures do not detect it. Detection requires PowerShell ScriptBlock Logging (Event ID 4104), AMSI (Antimalware Scan Interface) integration, and behavioral monitoring of LSASS access patterns. Organizations should ensure PowerShell logging is enabled at the ScriptBlock level and that security tools can inspect in-memory PowerShell execution.
Can Windows Defender detect Mimikatz?
Yes, Windows Defender detects known Mimikatz binaries and flags them as HackTool:Win32/Mimikatz. For the stock, unmodified Mimikatz executable, Windows Defender provides reliable detection. However, attackers routinely bypass signature-based detection through several techniques including binary modification, custom compilation from source, PowerShell-based execution (Invoke-Mimikatz), renamed executables, and reflective DLL injection. Red Canary's 2026 report emphasizes that traditional detection methods for LSASS-abusing tools are "far behind" current attacker capabilities. This does not mean Windows Defender is useless — it catches unsophisticated attacks and automated scripts. But organizations should not rely on it as their sole Mimikatz defense. Behavioral detection that monitors LSASS access patterns, regardless of what tool triggers them, provides far more reliable coverage.